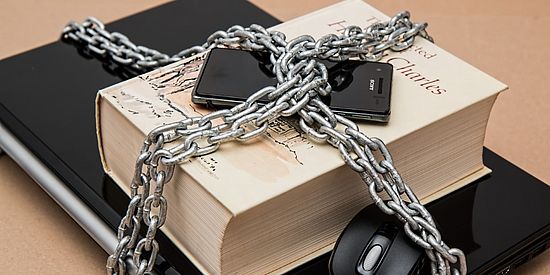
Data security
What has to be considered when dealing with particularly sensitive data?
Computers on which particularly confidential data that needs to be protected is stored require special access protection. This protection concerns physical access to the computer, access to the operating system and access to data.
Rooms with computers containing data worthy of protection must be locked when leaving. Such rooms should only be accessible to authorised persons and the computers must be specially secured against theft.
Existing mechanisms to ensure that only authorized users have access to the operating system must be used. These include:
- Startup protection (bio-passwords)
- Exclusive use of operating systems with user authentication
- Authentication via passwords
The use of strong passwords according to the password guidelines is mandatory. If possible, a combination of several methods should be used for authentication: Knowledge (password), Possession (token, smart card) and Property (biometric). Even when leaving the workplace for only a short time, the computer must be secured (screenlock with password protection).
Encryption of particularly confidential and sensitive data should be carried out using an up-to-date encryption system.
Computers with particularly confidential and sensitive data should not be connected to the Uninetz. If this cannot be avoided, such data must never be accessible on a generally accessible network drive. Data of this category may only be transmitted electronically with an up-to-date encryption system.
On mobile devices, particularly sensitive data may only be stored in encrypted form.
Printers and faxes on which particularly confidential and sensitive data are printed must not be located in freely accessible places or must have functions for secure printing (collection by the person using the printer).
Secure deletion and overwriting of particularly confidential and sensitive data on hard disks, floppy disks or backup media is imperative. Data that is no longer required must be securely deleted.
Old data carriers such as hard disks, CDs, floppy disks or tapes may still contain sensitive, confidential or secret data. Improper disposal or passing on of such data carriers is dangerous and should be avoided!
Attention: if you send in defective data carriers for a warranty exchange, they may be repaired and later supplied to other customers as replacement equipment!
Destruction by outsourcing
In the anteroom of IT-Services there is a locked container of the company Reisswolf. This is emptied regularly and the data media are destroyed in accordance with the law. University data media to be destroyed can be disposed of here. You can shred CDs and DVDs yourself.
Quick Links
